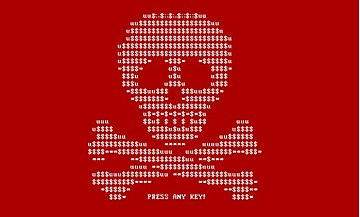
 Today, 27 June 2017, a new malware has begun attacking networks around the world. Petya, also known as Petrwrap, is the name and encrypting your information is its game. It has shown itself to be different than other ransomware of late. This one does not encrypt files one at a time but denies user access to the full system. The creators of Petya produced a small kernel that is only 32 sectors in length and made their own boot loader.
Today, 27 June 2017, a new malware has begun attacking networks around the world. Petya, also known as Petrwrap, is the name and encrypting your information is its game. It has shown itself to be different than other ransomware of late. This one does not encrypt files one at a time but denies user access to the full system. The creators of Petya produced a small kernel that is only 32 sectors in length and made their own boot loader.
How does it work?
Petya reboots the user’s computer and encrypts the master file table (MFT) which makes the master boot record (MBR) inoperable. This stops all access to the system and displays a ransom note. The computer can’t be rebooted once it has been infected. Recent information has stated that Petya is using a fake Windows certificate that is typically used by an internal tool. This tactic makes Petya extremely dangerous and shows the risks of an unpatched system.
What Can Be Done About It?
Petya exploits vulnerabilities in SMBv1 and takes advantage of unpatched Windows systems. Protect your environment by disabling SMBv1 and update using the newest patches provided for your operating system. The ransomware is most dangerous after it reboots the user’s system. To prevent that from happening it would be prudent to turn off the setting that restarts the computer after a system failure. The reasoning is if Petya is detected in Stage 1 there is still a good chance the data can be recovered.
Technical Details
- Disabling SMBv1
- Disable Automatic Restart on System Failure
The following links contain information about the exploit and fixes.
UPDATE: 6/27/2017 4:10PM CST
This is not just a new variant or wrapper around Petya but appears to be a completely new variant that simply uses the Petya encryption mechanism. The malware appears to be using both SMBv1 and brute force attacks against externally exposed RDP services. The malware is currently charging the equivalent of $300.00 USD of BitCoin and has collected roughly $10,000 USD as of 5:00 PM EST. The e-mail address associated with the ransomware has been disabled by the e-mail service provider, so those who are paying the ransom are unable to communicate with the attackers to get their decryption key.
There is a temporary fix that will prevent systems from getting infected. The malware before encryption searches for a file c:\Windows\perfc . If this file exists the malware will not begin its encryption routine and the system will not be impacted. With a minor update, this fix would be bypassed but for this initial wave, it will prevent infection.